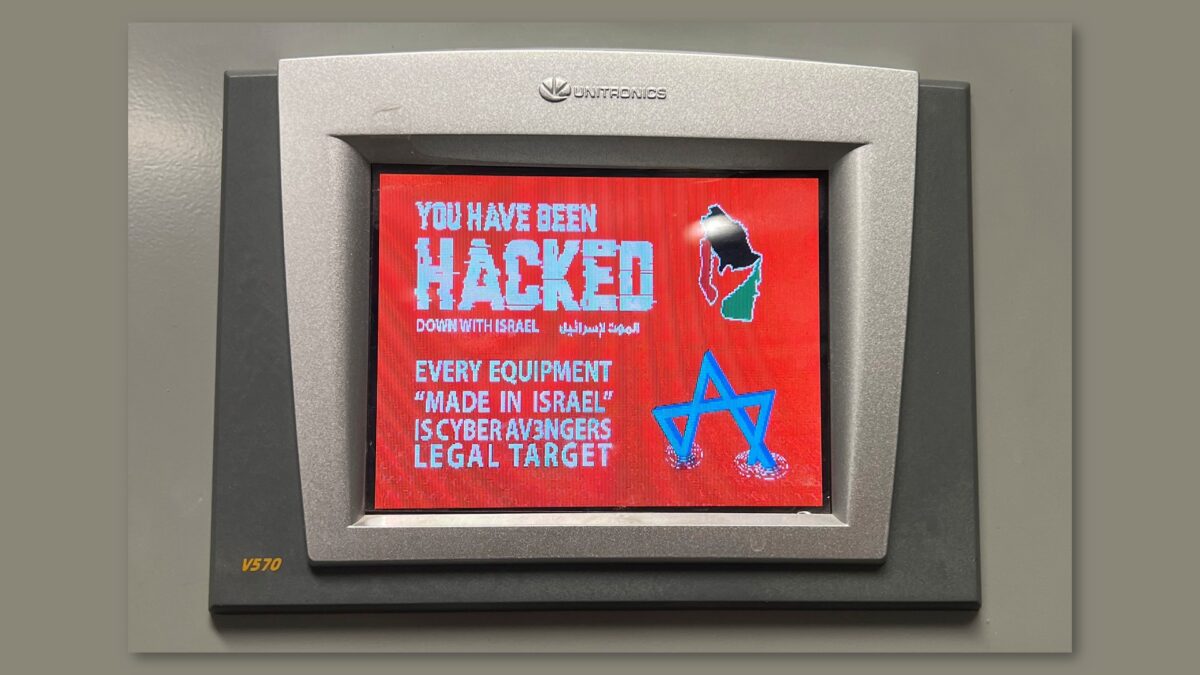
This page summarises some of the most recent cyber attacks on water and wastewater utilities that are in the public record. The majority of organisations, of any type, prefer not to publicly report their incidents, so the reality is that more attacks are occurring than we hear about. American Water Date: October 2024Country: United StatesConsequence: […]